Hackers Seize $32 Million in Ethereum in Parity Wallet Breach

Parity Technologies has issued a critical security alert for its popular multi-signature wallet software following an apparent breach. The development team urged users holding ether in multi-sig contract wallets version 1.5 or later to immediately transfer their tokens to a secure address. The breach only affects multi-sig wallets; normal wallets appear to be safe.
https://twitter.com/jutta_steiner/status/887764178479566848
Hacker Nets $32 Million Windfall
According to Etherscan.io , the hacker(s) absconded with more than 153,000 ether, worth more than $32 million at the current exchange rate ($213 per CoinMarketCap). The Parity wallet hack comes just days after CoinDash had to cancel its much-hyped ICO following a $10 million hack.
It’s worth noting that the DAO hack–which ultimately resulted in an Ethereum blockchain split–netted hackers $50 million in tokens at the time.

Non-ether tokens held in multi-sig wallets are also subject to the vulnerability, but the hacker only stole a small amount of one token–FUCKcoin.
Developers Scramble to Secure Funds
News of the hack quickly spread throughout the cryptocurrency ecosystem, and Ethereum projects storing funds in Parity multi-sig wallets scrambled to see if their funds had been compromised. Swarm City confirmed they had lost more than 44,000 ETH in the breach and revealed that funds held by Edgeless Casino and Aeternity had fallen prey to the hacker as well. Others, such as CivicKey CEO Vinny Lingham, breathed a sigh of relief after finding their tokens were safe.
White Hat Group Drains Vulnerable Wallets
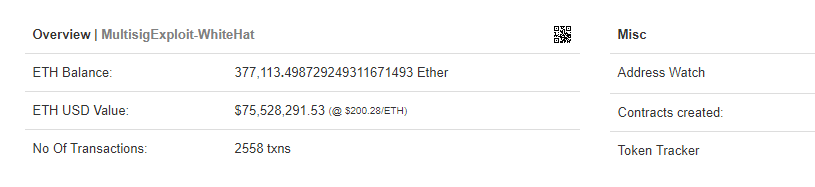
Parity later announced that, following the hack, the White Hat Group quickly began to drain as many multi-sig wallets as possible to prevent the hackers from making off with any more funds. The group is currently holding approximately 377,000 ETH–as well as 33 different tokens–in a secure wallet while they create replacement wallets.
The White Hat Group warned fundholders to be patient as they worked through the issue. As they stated on Reddit :
If you hold a multisig contract that was drained, please be patient. We will be creating another multisig for you that has the same settings as your old multisig but with the vulnerability removed and we will return your funds to you there. We will be using the donations sent to us from The DAO Rescue to pay for gas….Effectively we will upgrade your multisig contract for you, all you will have to do is, be patient, find your new multisig address once we have finished, and it will be like nothing happened.
Hacker’s Paradise?
The Parity hack sparked criticisms of Ethereum and Solidity–its programming language–from some corners of the cryptocurrency community. Several Twitter users posted screenshots of the Parity website, which boasts about their quality control process:
Every single line in our codebase is fully reviewed by at least one expert developer (and routinely two or more) before being placed in the main repository.
Litecoin developer Charlie Lee opined that the breach “pretty much confirms that Ethereum is hacker paradise.”
Don’t Fall Prey to Phishing Attempts
With a breach as high-profile as this one, malicious individuals are almost certain to exploit the opportunity to steal even more funds. Avoid falling prey to phishing attacks by carefully analyzing emails and links before you click on them, and remember that this breach is localized to Parity multi-signature wallets version 1.5 or higher; no other ethereum wallets were affected.
Featured image from Shutterstock.