Stealth Payments Create Anonymous Bitcoin Transactions

 Stealth payments are a technique for protecting the privacy of recipients in a Bitcoin Transaction. So-called “standard” transactions are pseudonymous. ECDSA key pairs abstract the identity of users. No mechanism exists to hide or encrypt standard transaction information in the block chain.
Stealth payments are a technique for protecting the privacy of recipients in a Bitcoin Transaction. So-called “standard” transactions are pseudonymous. ECDSA key pairs abstract the identity of users. No mechanism exists to hide or encrypt standard transaction information in the block chain.
With stealth payments the exception, full transaction history is available for every Bitcoin address. A service like Blockchain.info is able to calculate balances this way.
Conceptualized for Bitcoin by Peter Todd, but first mentioned in ByteCoin , Stealth Transactions enable stealth payments. The data for these payments is public. However, using a little cryptographic black magic , the transaction remains anonymous.
For example, 6ea5c6f1a97f382f87523d13ef9f2ef17b828607107efdbba42a80b8a6555356
The Diffie–Hellman Key Exchange
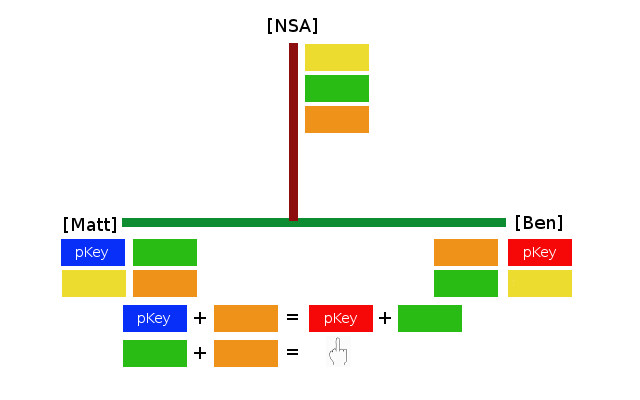
Stealth payments are an ingenious implementation of a Diffie-Hellman (DF) key exchange. The classic explanation of DF goes as follows:
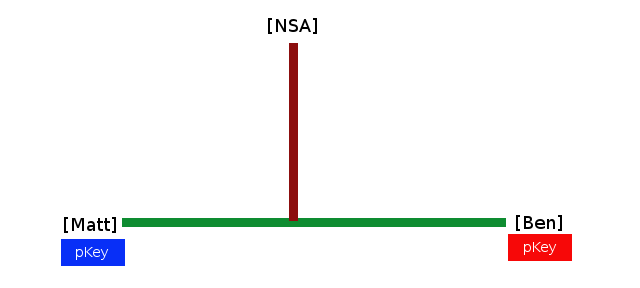
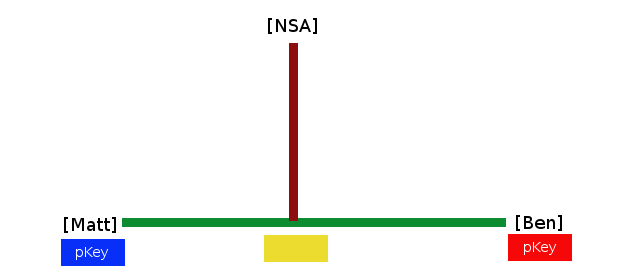
1.) Matt and Ben are communicating over a medium. A third party, the most benevolent spy organization in the world, is eavesdropping. Matt and Ben would like to share some color secretly.
2.) Publicly, they agree on a color and exchange it with one another.
3.) Matt, Ben, and anyone else listening know the shared color.
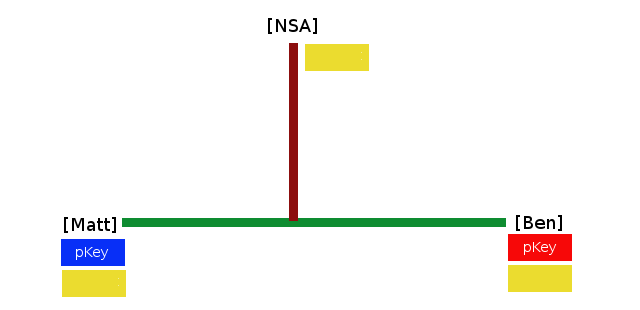
4.) Matt and Ben mix their private colors with a shared color. Each is creating a new, unique, color mixture.
5.) The new colors are exchanged.
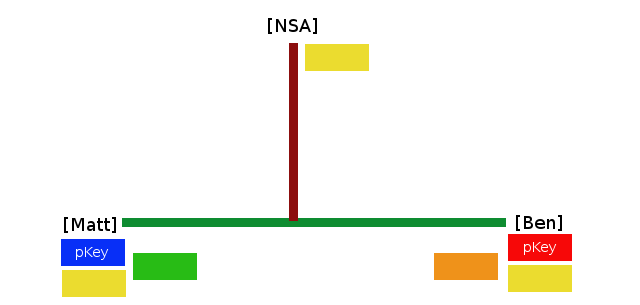
6.) Now, Matt and Ben mix their private keys with the color mixture from the other. It will be the same color every time.
Matt’s Final Color: Blue + Yellow + Red
Ben’s Final Color: Red + Yellow + Blue
Eavesdropper’s Final Color: Yellow + Blue + Yellow + Red + Yellow -or- Yellow + Green + Orange
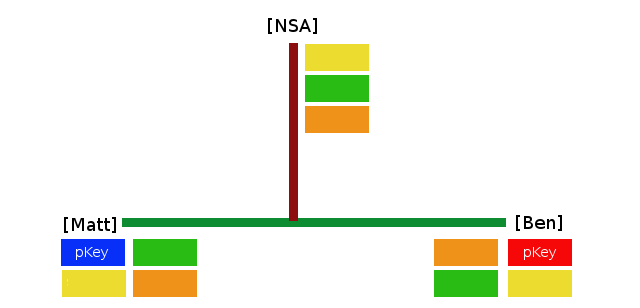
It is physically impossible for the Eavesdropper to ascertain the final color. That is a secret shared between Matt and Ben.
Also read, xHamster Porn Site Helps You and Bitcoin “Rise a Little Bit”
Modular Arithmetic
Diffie-Hellman uses modular arithmetic. The Yellow color represents the formula G mod P
G: The Generator, is the primitive root of P
P: A Frickin’ Big Prime Number
The formula works such that when G is raised to any power between 1 and P it has the same chance of being any number between 1 and P as any other. Also, no output will repeat within the range, 1…P. In addition to being an awkward sentence, it’s a slippery concept. Also, easier to show.
G mod P
G mod P is a finite field. If the exponent were to go above the prime, it wraps. That makes ’19’ equivalent to ‘1’; ’20’ to ‘2’; etc.
In the color example:
G mod P
Matt’s pKey: 28
Ben’s pKey: 5
2^28 mod 19 = 17
2^5 mod 19 = 13
17^5 mod 19 = 6
13^28 mod 19 = 6
Making Stealth Payments
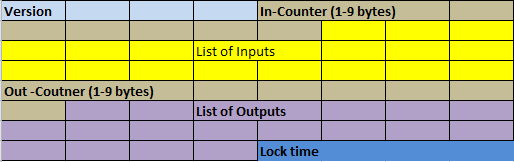
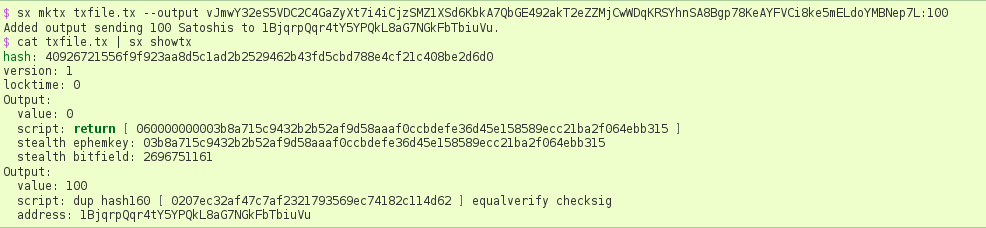
A standard Bitcoin Transaction contains a list of inputs and a list of outputs. In a stealth payment, the transaction outputs come in pairs. The first output contains stealth metadata. The recipient of the payment combines their stealth keys with the metadata to generate a private key.
The second output is the same as a standard transaction’s output. However, in a stealth payment, the second output is paid to the address for the private key hidden in the first output’s metadata.
1.) Alice generates a new stealth address
The SCAN_SECRET and SPEND_SECRET keys are used to generate the stealth address.
2.) Bob uses Alice’s stealth address to create a transaction
Bob will generate an ephemeral key. An address is created using Alice’s stealth key and the ephemeral key. The second output will pay to this address.
3.) Alice scans the block chain looking for a matching address.
Using the ephemeral key in the metadata, and her stealth address Alice can generate addresses similar to Bob in step 2. If Alice finds a matching address, it means the transaction belongs to her.
Also read, Two Cloudmining Platforms, Hashie and LTCGear, Mysteriously Offline
4.) Alice exports the private key
That’s how you make a stealth payment. Obviously, scanning the entire blockchain checking for outputs isn’t practical. In the future, as stealth payment volume increases, transaction can be sharded – split into parts. Cutting down on the scanning.
It’s impossible to tell Alice received a payment from Bob. Anyone parsing the blockchain would just see the stealth payment data in the second step. Alice becomes the anonymous recipient of a payment from Bob.
Stealth payments put the responsibility of generating key pairs on the buyer. Effectively, a stealth payment is like burying a treasure chest and marking the location with a pirate symbol. The symbol indicates which pirate can unlock the chest. However, no one knows which pirates the symbols belong to.
The following wallet software support stealth payments
sx
What Do You Think? Comment Below.
Images from the author, sx and Shutterstock